CYD Campus BACS Hackathon 2025 - Exploring Security for Building Automation and Control Systems
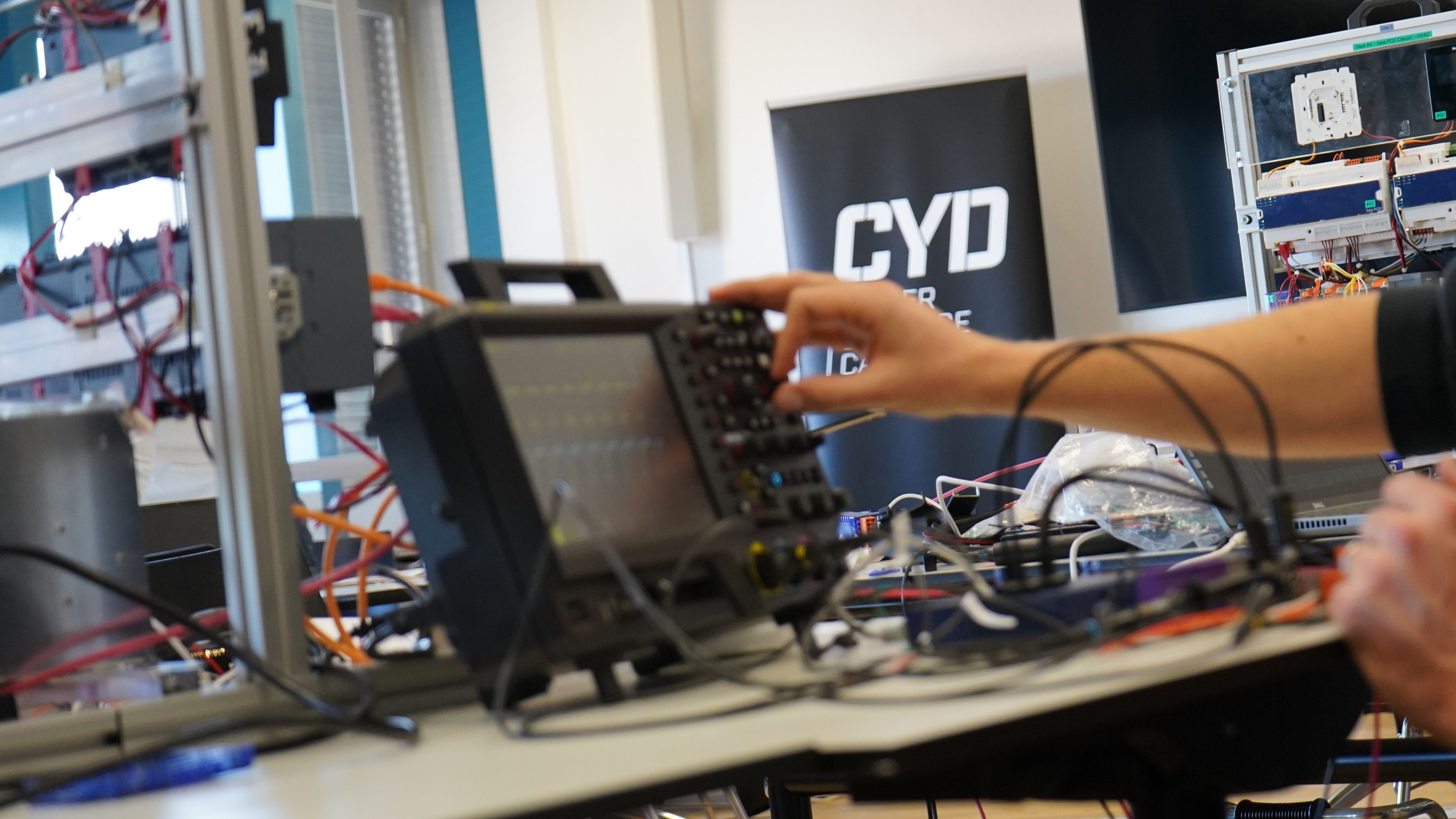
From February 3rd to 7th, the BACS (building automation and control systems) hackathon of the Cyber-Defence Campus (CYD Campus) by armasuisse Science and Technology (S+T) took place in Thun. Participants had the opportunity to test real HVAC (Heating, Ventilation, and Air Conditioning) systems, analyze security vulnerabilities, and develop defense strategies. In addition to an open research track, the event offered intensive training in firmware analysis and network security. The focus was on expert exchange and interdisciplinary collaboration.
Andrea Thäler, Cybersecurity and Data Science, armasuisse Science and Technology
In brief
This edition focused especially on the cybersecurity of building automation and control systems (BACS). Eventhough BACS are widely used in modern buildings, research has been limited so far. Thus, the BACS hackathon organized by Cyber-Defence Campus (CYD Campus) of armasuisse Science and Technology (S+T) opend up the opportunity to make us of cybersecurity methods to further explore this issue.
The aim of this hackathon was to launch a research initiative on the cybersecurity of building automation and control systems (BACS). These systems are widespread, rarely updated, and often not managed by IT departments. The lack of security research and understanding of these systems poses a significant risk. This is why the hackathon was created: to bring together vendors, building automation specialists, cybersecurity researchers, and academics for a week of testing, experimentation, and learning about the security of BACS.
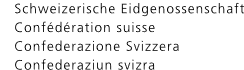
To facilitate the hackathon’s objectives, participants had access to over a hundred devices and systems. These were configured to replicate a real-world environment, complete with lights, presence sensors, valves, thermostats, and more. The systems were designed to simulate actual installations, providing participants with the freedom to interact with them and explore various aspects of building automation and control.
Key Findings and Surprising Discoveries
The hackathon yielded several unexpected discoveries, showcasing the creativity and expertise of the participants. Participants were able to profit from a lack of integrity checks on a device firmware to modify it, allowing to display arbitrary messages and change its behavior to enable administrative features. To demonstrate having control over the device, they made it display arbitrary text on its screen. Other participants focused on testing management interfaces using network traffic protocol fuzzing, which produced positive results by uncovering weaknesses in the system’s communication protocols. Additionally, some teams developed software implementations of management protocols that allowed researchers to manually craft network packets, offering a deeper level of control over system interactions. These discoveries provided valuable insights into the vulnerabilities present in building automation and control systems, paving the way for future research and improvements in security.
‹Fuzzing› is a software testing technique used to identify vulnerabilities and bugs by inputting random, unexpected, or malformed data (known as "fuzz") into a program or system.
An Innovative Test Environment for Research and Learning
To ensure participants had a hands-on learning experience, the BACS hackathon provided a very well equipped test environment. This included real-world HVAC systems from various manufacturers, as well as standalone gateways and devices for testing. The event was split into two parallel tracks: a Training Track and an Open Research & Tooling Track. The Training Track allowed participants to gain practical skills in firmware analysis and network security protocols. On the other hand, the Open Research & Tooling Track encouraged participants to dive deeper into the security of BACS. In this track, the research was divided into offensive and defensive strategies: the offensive side focused on discovering and exploiting vulnerabilities in devices and protocols, while the defensive side concentrated on developing protection mechanisms, testing detection tools, and implementing measures to harden systems against attacks. Together, these tracks fostered an environment where learning and innovation were at the forefront of BACS cybersecurity.
Future prospects
BACS are now ubiquitous in modern buildings, yet their security has historically been low. Fortunately, the industry has begun to adopt secure development practices and standards such as ISA/IEC 62443 and new protocols like BACnet/SC. However, these solutions are not yet widely used and therefore are not well tested in practice. As a consequence, their maturity is limited, especially with regard to efficient security management of BACS, and public security research on BACS remains limited. This is why the CYD Campus organized the BACS hackathon, to foster collaboration between researchers, industry, and security experts to push for more security and innovative security solutions.
ISA/IEC 62443 is a series of international standards for industrial automation and control systems (IACS) cybersecurity. It was developed to address the security concerns of systems that manage critical infrastructure, such as manufacturing facilities, utilities, and building automation systems.
All discovered security issues will be disclosed by the Cyber-Defence Campus to the respective manufacturers via the National Cyber Security Centre (NCSC).